Advanced Encryption Standard (AES)
Advanced Encryption Standard, a symmetric key algorithm, implemented in C++. All the parties use the same key for encryption and decryption. It has superseded DES, another symmetric key algorithms.
About
Rijndael was selected by NIST (National Institute of Standards and Technology) as AES. Unlike Rijndael in which block length and key length can be specified to any multiple of 32 bits, AES fixes block length to 128 bits and key length to (128 or 192 or 256) bits.
Description
The total number of rounds with key of 128 bits is 10. There are four subroutine that are performed in each rounds.
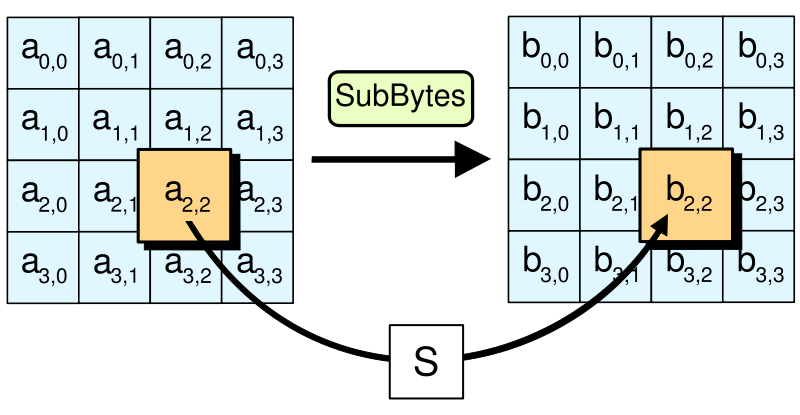
- Byte Substitution Transformation
Each element of state is non-linearly mapped to corresponding element in the s-bx. 1
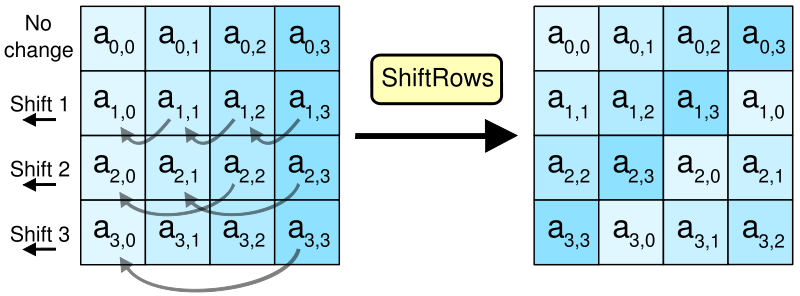
- Shift Rows
Rows are cyclically shifted to the left with offset of 0, 1, 2, 3 for rows of 1, 2, 3 and 4 respectively. 2
- Mix columns 3
Each new column (ro, r1, r2, r3) is generated from old column (a0, a1, a2, a3).
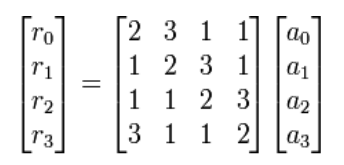
Here, r0 = {2 . a0} + {3 . a1} + {1 . a2} + {1. a3} r1 = {1 . a0} + {2 . a1} + {3 . a2} + {1. a3} r2 = {1 . a0} + {1 . a1} + {2 . a2} + {1 . a3} r3 = {3 . a0} + {1 . a1} + {1 . a2} + {2 . a3}
- Add Round Key
For each round, subkey is combined with the state matrix using biwise XOR.
Key Generation
Initial key is described as a state matrix.
| Co | C1 | C2 | C3 |
|---|---|---|---|
| a00 | a01 | a02 | a03 |
| b10 | b11 | b12 | b13 |
| c20 | c21 | c22 | c23 |
| d30 | d31 | d32 | d33 |
The last column is cyclically rotated to move the last block to the top.
| Co | C1 | C2 | C3 |
|---|---|---|---|
| a00 | a01 | a02 | d33 |
| b10 | b11 | b12 | a03 |
| c20 | c21 | c22 | b13 |
| d30 | d31 | d32 | c23 |
The last column is then mapped with the corresponding element of the s-box.
| C3 | C3' | |
|---|---|---|
| a00 | –> | a02 |
| b10 | –> | b12 |
| c20 | –> | c22 |
| d30 | –> | d32 |
New column C0 is generated by XORing previous C0 with the new column.
| C0 | C3' | |
|---|---|---|
| a00 | ⊕ | a02 |
| b10 | ⊕ | b12 |
| c20 | ⊕ | c22 |
| d30 | ⊕ | d32 |
Similarly all new coulumns are generated by XORing with pervious columns.
comments powered by Disqus